VA Nominee Tanya Bradsher in Hot Water: Inside the Brewing IT Scandal & Its Implications for Veterans
In the heart of Capitol Hill, another scandal is brewing. This isn’t your typical front-page scoop. This is a potential dereliction of duty that the Biden Administration can ill afford in the nomination of Tanya Bradsher.
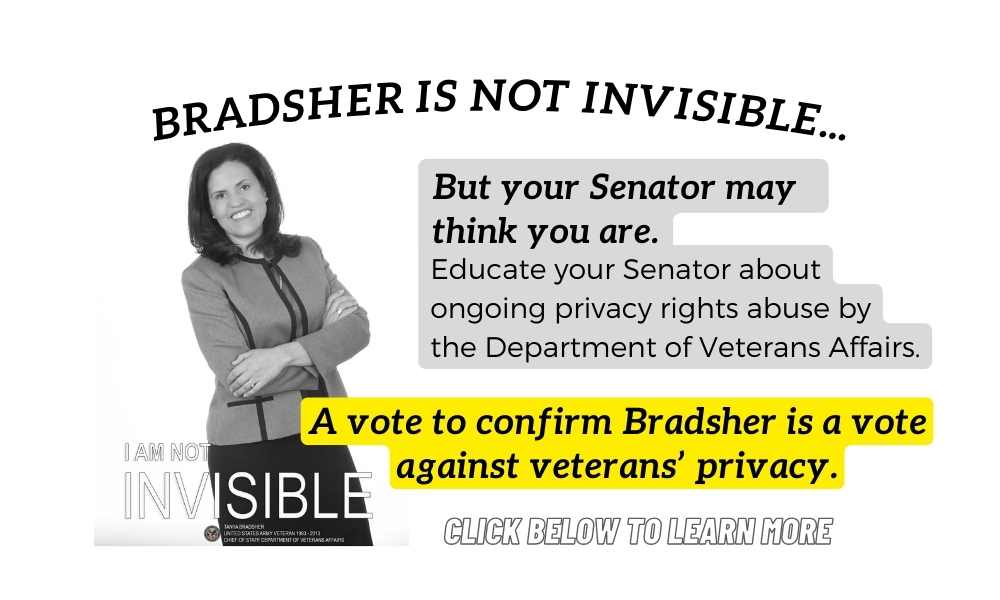
VA Deputy Secretary nominee Tanya Bradsher, poised to assume one of the most consequential roles at the Department of Veterans Affairs, is under the spotlight for not just an IT data breach but the allegations of “misleading” the Senate in her statements about it.
At the center of the scandal are VA Integrated Enterprise Workflow Solution (VIEWS), the agency’s VA Office of Information Technology (OIT), and the VA Chief of Staff Tanya Bradsher who is responsible for all agency correspondence management.
Bradsher is not just responsible for correspondence management. She was obligated to provide correct and factual statements to the Senate when asked about an ongoing whistleblower VIEWS investigation. Whistleblowers seeking help to protect their confidential information came to her more than one year ago, and how she managed the problem is a key variable for many considering her nomination.
Yesterday, the Senate accelerated the confirmation vote of Bradsher to next week even though Bradsher and VA have not finalized their report addressing the extent of the alleged data breach. Information about the breach and Bradsher’s management of it will be laid out bare in the final Office of Special Counsel’s own report.
Don’t veterans deserve to know the truth before the Senate votes?
A draft of the VIEWS – VA OIT report has been released by one of the whistleblowers, Peter Rizzo, a certified fraud examiner who used to work at the VA. He felt forced to release the draft report and his formal comments to ensure members of the public and Senators were fully aware of the scope of the issue.
And how could they? The Senate majority leader Senator Jon Tester (D-MT) in the Senate Committee on Veterans Affairs refused to meet with VA whistleblowers about the data breach. Nothing to see here. Head in the sand. Just push through another scandal-mired VA nominee before anyone wakes up.
What’s the worst thing that can happen? Another IT scandal mismanaged by inept VA leadership? Thousands if not hundreds of thousands of veterans’ sensitive personal information has not been properly used or secured and millions in taxpayer dollars may be required to cover data breach fines in future litigation.
Senator Chuck Grassley (R-IA) has been fighting for veterans’ privacy, exposing this scandal for months. What has your Senator been doing?
Here’s what you need to know:
- Investigation Integrity: Bradsher, in her capacity as the VA Chief of Staff, faced intense scrutiny this summer regarding the IT data breach. Instead of adhering to legal mandates that require an external, unbiased review for such breaches, the VA opted for a self-assessment that was consented to by the Office of Special Counsel (OSC). This raises questions about the integrity and transparency of the investigation, particularly as policy changes coincided with the release of a condemning draft audit report.
- Opaque Reporting: The VA OIT’s report on the VIEWS system appeared deliberately confusing, and it falsely claimed there was no evidence of a data breach. There was evidence, the VA just redrafted its data breach policy and redefined breach definitions days before the report was released. Nothing to see here. Though the report did validate several allegations of misdeeds and breaches of the Privacy Act, the report embedded crucial findings deep within, forcing readers to navigate an extensive seven-page introduction to get to the heart of the 23-page document.
- Expanding Responsibilities: Bradsher’s current duties involve the VA Integrated Enterprise Workflow Solution (VIEWS). Should she be confirmed, she will gain a more significant role in supervising the tumultuous Cerner/Oracle electronic health record system. This ongoing scandal, which affects the communication lines between Congress, the public, veterans, whistleblowers, and VA leadership, makes her potential confirmation contentious.
- Inside Information: Whistleblower Peter Rizzo, with his background as a VA employee and as a certified fraud examiner, shared the VA OIT draft report and his insights with DisabledVeterans.org. As these details have only recently come to light, there’s concern that the gravity of the VIEWS scandal and Bradsher’s purported legal breaches might be underestimated by Senate members.
- History Repeats?: The Deputy Secretary role that Bradsher is vying for was previously occupied by Donald Remy, whose tenure ended abruptly in April. Remy’s initial nomination a decade ago by the Obama Administration was retracted due to credibility concerns. Despite being given another opportunity, Remy’s term was short-lived, raising questions about the selection process and the integrity of the position’s occupants.
- Senate Scrutiny: Senator Chuck Grassley (R-IA) has been forthright in his criticisms. He’s challenged Bradsher on her potential misleading statements presented to the Senate Committee on Veterans Affairs. The crux of his apprehensions lies in Bradsher’s potential inconsistencies concerning the security flaws in the VIEWS system.
- Veteran Impact: The IT scandal not only threatens the integrity of the VA’s systems but also poses significant risks to veterans’ personal data and trust. As veterans rely on the VA for essential services and support, any breach or mishandling of information can directly compromise their privacy, security, and faith in the institution dedicated to their well-being.
RELATED: Veterans Affairs Security Breaches Can’t Be Ignored
Deep Dive into the VA OIT Report on VIEWS
This scandal comes on the heels of another IT scandal where 57,000 veterans received delayed benefits adjudications, some lasting years, because of a glitch in VA benefits processing systems.
Nominees matter. The new head of the Veterans Benefits Administration (VBA), Joshua Jacobs, was confirmed using cloture despite allegations of lack of candor and despite limited experience in a leadership role of that type or responsibility. Apparently, candor and credentials no longer matter to this Senate, but they used to in the days of the late Senator John McCain.
More on this below and how it impacted former VA Deputy Secretary Donald Remy in 2009.
RELATED: Army Lawyer Pick [Donald Remy] Faces Resume Flap
Despite slick wording to confuse readers with qualifying language, the VA OIT report on VIEWS paints a concerning picture of systemic weaknesses at VA:
- Since 2018, the VA has consistently neglected legally required measures to safeguard the confidentiality of veteran and whistleblower PII, breaching the Privacy Act of 1974 and the Whistleblower Protection Act.
- VIEWS was designed to manage correspondence for the White House complaint hotline initiated in 2017, but it was expanded in 2018 to replace VA Internet Quorum, ExecVA, and other systems of records without timely notice to Congress through notice and comment.
- It has been evident that many cases contained sensitive personal and whistleblower data that wasn’t adequately shielded from unauthorized access.
- Key figures in VA leadership, including the OGC, had been aware of confirmed data breaches since 2019, yet comprehensive data security measures remained unimplemented, and those individuals impacted were not timely notified.
- Despite demands from the OSC, the VA still hadn’t fully secured the confidential data by July 2023.
- As of 2023, no effective systems were in place to monitor data breach mitigation efforts or detect their efficacy, after running the system of records for five years.
- The VA did not conduct proper privacy assessment processes to minimize privacy and security threats to sensitive information consistent with legal and policy requirements.
- Essential log files for performing a Privacy Impact Assessment, vital for a system of records notice, couldn’t be accessed to gauge the extent of unlawful record access, but that did not stop VA from stating data breach was “not substantiated” when the allegation was truly “not investigated” with necessary evidence.
- Historic assessment and approval documents were missing from the Enterprise Mission Assurance Support Service (eMASS), and no effort seemed to be made to locate copies elsewhere within the VA for the report.
- VIEWS did not undergo the mandatory Privacy Threshold Analysis and Privacy Impact Assessment until 2021.
- Only in 2022 was a required System of Records Notice regarding VIEWS made public in the Federal Register for transparency and public feedback, not in 2018.
- Critical privacy impact documents failed to acknowledge or address the fact that whistleblower identifications were being received, collected, or stored within VIEWS.
Furthermore, by knowingly violating the Privacy Act of 1974, the agency and its officials not only jeopardize their professional integrity but also expose themselves to significant legal risks, including potential penalties and liabilities. At stake is more than just the reputation of a nominee; it’s the trust and confidence of countless veterans and whistleblowers who depend on the VA’s integrity and honesty.
The Senate has a responsibility to respond promptly and firmly. Every moment counts.
Now What?
Take a Stand for Veterans On Tanya Bradsher Vote: Rally with Digital Power!
If you’ve delved this deep into the article, it’s evident that this issue resonates with you. From the outset, Bradsher’s qualifications for her position seemed questionable. But now, with the revelations from the VIEWS responses, it’s clear that there’s more at play.
Bradsher’s ‘golly gee’ demeanor during her confirmation hearing was seemingly nothing more than a smokescreen. And despite her assurances to the Senate about taking responsibility, her recent actions with regard to the VIEWS system suggest otherwise.
Here’s How YOU Can Make a Difference:
- Connect Directly with Decision Makers: If this issue stirs you, don’t let your voice go unheard. Reach out directly to the offices of influential US Senators. Share this article and the linked VA OIT draft report. Your voice matters. Let’s ensure they know veterans deserve better.
- Craft Your Social Media Message: Use platforms like Twitter, Facebook, and Instagram to raise awareness. Here are some sample messages you can use:
- 🚨 “Veterans deserve leaders who prioritize their needs over politics. Concerned about the VA scandal? Read more here. #VAVIEWSConcern #VeteransFirst” [Link to Article]
- 💡 “Join me in ensuring our veterans have leaders who truly care! Reach out to your senators now! #ActForVeterans” [Link to Article]
- 💌 “Our veterans have served us. Now, let’s serve them. Check out this concerning report and act! #VAOversight #StandWithVets” [Link to Article]
- Tag Key Senators: When posting on social media, tag influential senators like Senator Bernie Sanders, Senator Kyrsten Sinema, and Senator Joe Manchin. Use the power of public attention to ensure they’re aware of these concerns.
The digital age offers immense power at our fingertips. Let’s channel it effectively for the betterment of our veterans. Your involvement can spark the change we need. Stand with our veterans now! 🇺🇸
Only If You Want To Keep Reading
Here are some additional details the Senate and America need to know. The VA OIT draft report is at the bottom of this article as is the response of a certified fraud examiner. It’s not every day we see a response from a fraud expert hammering on VA IT foibles.
The Remy Coincidence: Senators, Take Note
Coincidentally, Bradsher is auditioning for the role previously held by Donald Remy, the last Deputy Secretary who was confirmed in 2021 who also quietly vacated the position in April.
Just over a decade earlier, Remy withdrew his nomination after being accused of a lack of candor to SVAC. The lifelong attorney worked at Fannie Mae for six years leading up to the 2008 Great Recession, and his decisions as a senior leader of the company became spotlighted following the subprime mortgage crisis leading to the 2007-08 Great Recession.
The issue?
Remy omitted his employment at Fannie Mae on the resume he provided to the Senate for consideration of his nomination. Remy was no ordinary employee. He was the chief compliance officer and general counsel of the massive mortgage company.
The Senate Armed Services Committee initiated questions led by the late Senator John McCain into disclosure of Fannie Mae’s multi-billion-dollar account errors in 2006.
According to the Washington Times:
But Donald M. Remy left out Fannie Mae’s name in a work history he recently sent to the Senate committee weighing his nomination as the Army’s general counsel.
Instead, Mr. Remy, 42, described Fannie Mae – which the government took over last year amid an accounting scandal – only as “a major U.S. company.” The same biography lists the names of Mr. Remy’s other past and current employers.
Mr. Remy, who worked at Fannie Mae from 2000 to 2006, has called the omission an oversight and said he is proud of his work for the agency.
His nomination is pending, but at least two Republican senators on the Senate Armed Services Committee – John McCain of Arizona and Mel Martinez of Florida – have raised questions about why Fannie Mae wasn’t included on Mr. Remy’s work history. The senators also want to know more about Mr. Remy’s duties at the company before Fannie Mae disclosed billions of dollars in accounting errors in 2006.
Citing “serious concerns” about Mr. Remy’s “lack of candor,” Mr. Martinez wants another hearing on the nomination, according to a letter he recently sent to Sen. Carl Levin, Michigan Democrat and chairman of the committee.
For Bradsher, we are not talking about a mere “resume flap” omitting reference to a prior employer. She made materially false statements about the security of the VA Secretary’s main correspondence system of records to the Senate in furtherance of her own ambitions.
There is no mystery or crystal ball needed to analyze how Bradsher will handle the Cerner/Oracle debacle or any other issue. She will shift blame and point fingers – that is what she is trained to do as a public affairs expert. She likely will not own up for any of her decisionmaking failures.
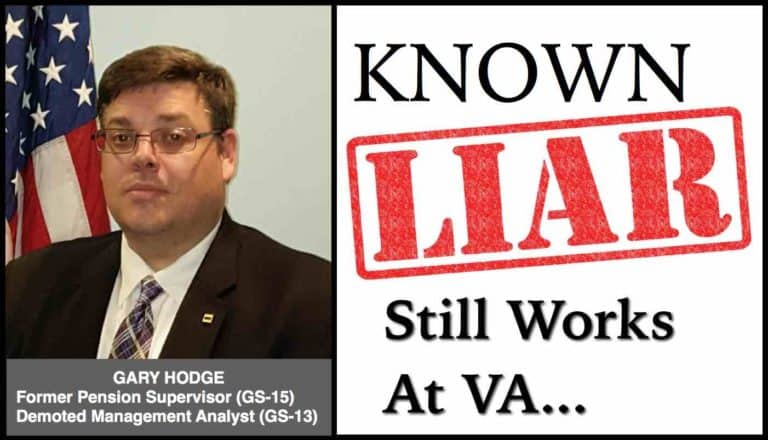
Look no further than the Executive Secretariate official who was quietly fired recently and replaced by a crony without publication of the open position, according to inside reports. But that official is not the responsible official, VA Chief of Staff Tanya Bradsher is, and she admits to being notified and delegating the matter to OIT.
RELATED: VA Chief of Staff Tanya Bradsher Selected For DINFOS Hall of Fame
Grassley Slams Tanya Bradsher Nomination, Urges Senate ‘No’ Vote
Yesterday, Senator Chuck Grassley (R-IA) drilled the nominee in a press release for a series of false and misleading statements she made in writing to Senate Committee on Veterans Affairs members this summer. His press release was not just based on the OIT report but also on the comments provided in response by Rizzo.
According to Sen Grassley:
I’ve just learned that the Majority Leader has filed for cloture on the nomination of Ms. Tanya Bradsher to be Deputy Secretary at the Department of Veterans Affairs. In addition to my remarks on the Senate floor on July 18, I’d like to provide more context to my decision to oppose her nomination, especially in light of new information that has come to my attention.
Ms. Bradsher, if confirmed, would be second in command at a deeply-troubled agency. Both the VA and Ms. Bradsher in her current role as chief of staff have shown repeated indifference to congressional oversight. Records show that she played a key role in the VA’s deficient response to my investigation of VA corruption that I launched in 2021. Another of my investigations has revealed that she also failed to secure sensitive veterans’ health information, PII, and whistleblower information in the VA’s correspondence system, VA Integrated Enterprise Workflow Solution, also called VIEWS, which is under her direct authority. My oversight has shown that VIEWS exposes veterans’ private and sensitive information to thousands of VA employees, only a small number of whom are authorized to see it. The VA and Ms. Bradsher provided misleading information about that as well, which I will discuss here.
[…]
As part of Ms. Bradsher’s Committee proceedings, she responded to questions for the record about veterans’ medical records stored in the VIEWS correspondence system at the VA. Ms. Bradsher provided misleading and often contradictory answers to senators’ questions. When asked about veterans’ medical records exposed in VIEWS, she responded that the VIEWS system doesn’t “handle” medical records. This was deeply misleading, as my staff had already verified that sensitive medical records are stored in VIEWS, and often exposed improperly for thousands of VA employees to see.
[…]
When whistleblowers last year informed the Office of Special Counsel (OSC) about these VIEWS privacy flaws, OSC found a “substantial likelihood of wrongdoing” related to potential violation of federal privacy laws. On August 2, 2022, OSC directed VA to investigate and report back within 60 days.
[…]
Even before Ms. Bradsher’s Committee hearing was held, the VA had already admitted to OSC that the VIEWS allegations raised by whistleblowers to Ms. Bradsher’s office last year were true. It’s not all in our imagination, as VA tried to mislead the U.S. Senate into thinking. The VA admitted as much in its own letter to OSC on May 26 of this year, before Ms. Bradsher’s VA Committee hearing, stating that the VA’s OSC-ordered investigation at the outset of its investigation had already “fully substantiated” allegations whistleblowers raised that, “VA officials are violating the Privacy Act of 1974 and the provisions of VA Directive 6502 and VA Handbook 6500 by improperly storing the personally identifiable information of whistleblowers, employees, and veterans in the Veterans Affairs Integrated Enterprise Workflow Solution (VIEWS) system of records because such sensitive information is not marked as sensitive and is therefore accessible to all VA employees that have access to VIEWS.” In other words, VA admitted that it violated federal privacy laws related to VIEWS by not securing sensitive data, but Ms. Bradsher withheld this key fact from the Committee when questioned, and the VA insinuated otherwise in its last-minute misleading memo circulated by the Committee majority on the eve of her Committee rubber stamp.
[…]
Despite their legal obligation to be candid with Congress and not to omit material facts from their statements to this body, this deeply-misleading memo to members of the Senate Veterans Affairs Committee right before their vote on Ms. Bradsher failed to even address the VA’s preliminary findings, and it misled the Committee by minimizing data security issues in VIEWS.
Certified Fraud Examiner Response To OIT Report
What follows is the response from Rizzo to OSC sent this month to address errors, omissions, and falsehoods in statements from VA:
I am writing to provide comment on a July 21, 2023 “Report to the Office of Special Counsel” by the U. S. Department of Veterans Affairs (VA) concerning OSC File Nos. DI- 22 – 000680, DI- 22 – 000682, and DI- 22 – 000742.
In late June 2022, while still employed by VA, two colleagues and I each filed separate whistleblower disclosures to the U. S. Office of Special Counsel (OSC) alleging that VA officials are violating the Privacy Act of 1974 and the provisions of VA Directive 6502 and VA Handbook 6500 by improperly storing the personally identifiable information of whistleblowers, employees, and veterans in the Veterans Affairs Integrated Enterprise Workflow Solution (VIEWS) system of records because such sensitive information is not marked as sensitive and is therefore accessible to all VA employees that have access to VIEWS.
After reviewing the evidence that my colleagues and I provided, OSC determined that there is a substantial likelihood of wrongdoing by VA. OSC subsequently referred the disclosures to VA Secretary Denis R. McDonough for investigation and report on or about August 2, 2022. It was not until July 21, 2023 — 353 days later — that VA finally issued its report to OSC. However, far more troubling is what VA officials did in that time period to evade culpability.
What follows is my analysis of VA’s July 21, 2023 report, which begins with my feedback on the report, followed by three additional recommendations for VA, and ends with three new allegations of wrongdoing by VA resulting from this investigation.
REPORT FEEDBACK
I would like to begin by thanking the investigator assigned to this case. I found him to be a consummate professional in all of my interactions.
Role of VA Office of Information & Technology (OIT): Aside from the shamelessly misleading Executive Summary, the body of VA’s July 21, 2023 report captures the myriad of very serious and consequential missteps by VA and Salesforce regarding the security of sensitive personal information. What I find most interesting is the role of OIT and the fact that this particular office was asked to investigate considering that the VIEWS system was created and is maintained pursuant to a contract with Salesforce that is managed through OIT. As effective as the investigator might have been, this arrangement creates the appearance of an ethical conflict and should have been avoided.
Data Breach: Page 17 of the report states, “It should be emphasized that there is no evidence that VIEWS vulnerabilities discussed in this report resulted in a privacy breach or has caused harm to Veterans, whistleblowers, or their families.” This finding is in error. Simply, the instant investigation did not examine privacy breaches and the harm caused to Veterans, whistleblowers, and their families due to VIEWS’ security flaws— the assigned investigator is
without the capacity, authority, training, and jurisdiction required to conduct such an investigation. Thus, VA has no basis to assert that there exists no evidence of a privacy breach or resulting harm.
Countless whistleblowers have come forward alleging otherwise unexplainable acts of retaliation, theft, vandalism, threats, and physical harm after blowing the whistle— VIEWS may very well be the source of information that fueled these illegal acts, but not until that is investigated properly will we know for certain.
Freedom of Information Act (FOIA) & Privacy Act Requests: VA claims it was “unable to substantiate” Allegation 3, which asserts that “VA officials have failed to include VIEWS in FOIA and Privacy Act requests, in violation of federal law and agency directive and handbook provisions.” This finding is invalid and should be changed to “Substantiated.”
First, consider that the report notes that VA’s FOIA Office pointed to only three instances in which VIEWS was searched for responsive documents even though VA processes many thousands of FOIA and Privacy Act requests annually.
Second, consider that in a FOIA request dated August 6, 2021, from Jason Foster of Empower Oversight, VA was asked to provide “all records relating to … [the VA’s] receipt of, discussions related to, processing of, and response to Senator Grassley’s April 2, 2021 letter to Secretary McDonough and/or his July 20, 2021 letter to Secretary McDonough.” VA’s response to this FOIA request failed to include responsive documents housed in VIEWS. I know this because I personally saw those records in VIEWS while employed at VA and have since come to learn that VA did not include them in its response to Mr. Foster.
Therefore, it can be substantiated that VA officials have failed to include VIEWS in FOIA and Privacy Act requests, in violation of federal law and agency directive and handbook provisions. Further, the fact that VA does not track Privacy Act requests globally is not a reason for VA not to examine this component of the allegation— this must be investigated broadly, as different VA offices may apply different practices.
ADDITIONAL RECOMMENDATIONS
Recommendation 1: Notify and provide credit protection services to those whose sensitive personal information was marked “not sensitive” in VIEWS.
Given VA and Salesforce’s years- long failure to secure sensitive personal information housed in the VIEWS system, the PII and PHI of potentially millions of Veterans and VA employees have long been freely available for the taking.
And no amount of training or annual affirmation of VA privacy policy by VIEWS users is going to prevent a bad actor from victimizing any of these individuals. As such, VA should be obligated to notify and provide identity theft protection to all Veterans and employees whose sensitive personal information was left exposed in VIEWS for any length of time. Through this report, VA has lost credibility with Veterans and employees, and restoring that trust involves more than fixing VIEWS— it requires the protection of those whose trust VA violated by making their PII and PHI available for more than 2,000 VA employees and contractors to see.
Recommendation 2: Reopen and revisit all whistleblower cases cited in VIEWS.
As a whistleblower myself, I am especially troubled by the report’s acknowledgement that “many thousands of [VIEWS cases] containing detailed information about VA employee whistleblower retaliation complaints [were] potentially accessible to the very people who were alleged to have committed wrongdoing” (p. 10). This conclusion alone obligates VA, OSC, and the U. S. Merit Systems Protection Board (MSPB) to reopen every whistleblower case referenced in VIEWS that was closed because the whistleblower was unable to prove that the retaliator had prior knowledge of the whistleblower’s protected activity.
Recommendation 3: Demand that Salesforce fix the security vulnerabilities of VIEWS at no additional cost.
On pages iv, v, 18, and 19, there are recommendations for VA to acquire “Einstein Data Detect,” a Salesforce product, to help protect privacy in VIEWS. It is difficult to understand why VA would pay Salesforce more money to acquire another Salesforce product to fix the security vulnerabilities of an existing Salesforce system (i.e., VIEWS). VA should enforce the terms of the existing contract and demand that Salesforce correct the problem at no further cost to the American taxpayer.
NEW ALLEGATIONS OF WRONGDOING BY VA
New Allegation 1: In its July 21, 2023 report, VA improperly used a three- week- old version of VA Handbook 6500.2 to draw findings on certain allegations from OSC File Nos. DI- 22 – 000680, DI- 22 – 000682, and DI- 22 – 000742, which was not the version of VA Handbook 6500. 2 in effect in August 2022 when OSC directed VA to investigate and report on the same allegations.
The conditions that led to the allegations of wrongdoing cited in OSC File Nos. DI- 22 – 000680, DI- 22 – 000682, and DI- 22 – 000742 existed when VA Handbook 6500.2 (March 12, 2019) was in effect. Further, that same handbook was in effect for nearly 11 months after OSC directed VA to investigate the allegations.
However, in what can only be described as an eleventh hour switcheroo, VA
brazenly replaced the contents of VA Handbook 6500.2 with a new version that coincidentally limits its liability in data security situations precisely like those that impacted the VIEWS system and disingenuously cited the revised VA Handbook 6500.2 language in its July 21, 2023 report without referencing its June 30, 2023 publication date or mentioning that an earlier version was in effect when OSC issued its order to investigate.
That VA evaluated the subject allegations in accordance with the three- week- old version of VA Handbook 6500.2, and not the one that was in place when the allegations were made, is wrong and should not be permitted. If left uncorrected, such would enable any agency or office accused of violating its own policies to modify said policies during an investigation to evade all liability. The consequences could be devastating to our nation.
New Allegation 2: VA executives conspired to delay publication of VA’s July 21, 2023 report to OSC and to modify VA Handbook 6500.2 to limit the possible findings of wrongdoing and recommended corrective actions in response to OSC File Nos. DI- 22 – 000680, DI- 22 – 000682, and DI- 22 – 000742.
VA was originally granted 60 days to respond to OSC’s demand for an investigation and report. However, VA repeatedly requested time extensions while it cobbled together a half- hearted solution in time for the report’s release. We also learned that VA bought time to water down the report’s language and even modify internal policy to soften the blow of the findings. All told, VA’s original 60 – day turnaround period turned into a 353 – day charade.
On June 30, 2023, VA’s Assistant Secretary for Information Technology published a
revised version of VA Handbook 6500 .2 (“Management of Breaches Involving Sensitive Personal Information”), which redefined the term “breach” such that VA’s failure to properly secure PII and PHI in its VIEWS system no longer qualifies as a “breach.” The most recent past version of VA Handbook 6500.2, dated March 12, 2019, defined the term “breach” as:
The potential acquisition, access, use, or disclosure of VA sensitive personal information in a manner not permitted by law or VA policy which compromises the security or privacy of that information.
However, the new version defines “breach” as:
A loss or theft of, or other unauthorized access to, other than an unauthorized access incidental to the scope of employment, data containing [sensitive personal information], in electronic or printed form, that results in the potential compromise of the confidentiality or integrity of the data.
Considering that this new definition (1) was issued just 21 days before VA published its July 21, 2023 report to OSC, and (2) specifically allows for the type of “incidental” access to PII and PHI that VA alleges in its July 21, 2023 report to represent the extent of access that occurred due to VIEWS system security failures, raises serious doubts as to the ethicality of this redefinition and indicates a concerted, coordinated effort by VA executives to protect themselves and VA given the seriousness of our allegations. Even more concerning i s that this VA policy change appears to be in violation of the Privacy Act, which does not allow agencies to evade responsibility for “incidental” disclosures of sensitive personal records.
New Allegation 3: VA’s new version of VA Handbook 6500. 2, dated June 30, 2023,
includes a revised definition of “breach” (vs. the definition in the previous version of VA Handbook 6500.2, dated March 12, 2019), such that it violates the ‘need to know’ provision of the Privacy Act (5 U. S. C. § 552a(b)(1)).
The Privacy Act states:
No agency shall disclose any record which is contained in a system of records by any means of communication to any person, or to another agency, except pursuant to a written request by, or with the prior written consent of, the individual to whom the record pertains unless the disclosure would be […] to those officers and employees of the agency which maintains the record who have a need for the record in the performance of their duties. 5 U. S. C. § 552a(b)(1)
Each time one of VA’s 2,000 + VIEWS system users accessed Veteran and Whistleblower PII and PHI through VIEWS, VA effectively disclosed that PII and PHI to the VIEWS system user. When that that disclosure is for a legitimate business purpose— for example, the disclosure of a Veteran’s social security number through the VIEWS system so the VIEWS system user could track down a separate record on behalf of the subject Veteran— there exists an obvious
“need to know” and thus, no violation of the Privacy Act. However, when that disclosure is unintentional or without a legitimate business purpose— such as when an unrelated VIEWS system user accesses the protected disclosures of a Whistleblower in VIEWS or when a VIEWS system user downloads and views the wrong Veteran’s DD- 214 — there exists no “need to know.”
Courts generally have found that intra- agency disclosures to employees that do not have a need for a given record in the performance of their duties are outside the scope of the “need to know” disclosure exception. Thus, by effectively allowing “incidental” disclosures of PII and PHI to employees who do not have a “need to know,” pursuant to the latest version of VA Handbook
6500.2, VA is operating in violation of the Privacy Act, which requires a “need to know” and provides no exceptions for “incidental” disclosures.
CONCLUSION
The mishandling of sensitive personal information occurred for three reasons. First, certain users were knowingly or inadvertently negligent in applying proper sensitivity thresholds to VIEWS system cases containing the PII and PHI of Veterans and VA employees despite VA security policy prohibiting such activity. Second, no technical controls were in place to prevent negligent users from failing to protect VIEWS system cases containing PII and PHI. Third, due to a lack of oversight, the VA Chief of Staff, VA Executive Secretariat, and OIT personnel failed to discover and secure sensitive personal information marked as “not sensitive” in VIEWS.
Thank you for providing this opportunity to respond to VA’s report.
*** End Rizzo Response ***
Final Thoughts On Bradsher And VIEWS Scandal
In light of these revelations, the role of every citizen and stakeholder in the democratic process becomes all the more pivotal. The strength of our democracy lies in the collective voice and active engagement of its citizens. As we navigate the complexities of this issue and determine the future course of the VA, it’s essential that our elected representatives hear from their constituents.
If you are as concerned about these allegations and the implications they hold for the VA, I urge you to reach out to your Senators. They need to hear from you – whether it’s through letters, emails, phone calls, or social media. Open dialogue and persistent engagement can shine a light on the issues, demand accountability, and catalyze positive change.
Remember, our veterans have given so much to serve our country. It’s now our turn to ensure that they receive the care, respect, and transparency they so rightfully deserve. Don’t stay silent. Let your voice be a beacon of change and a reminder to our elected officials that they must always prioritize the well-being of our veterans above all else.




We need to simply STOP! no one cares, no one listens to us Veterans no politician, Tester in moron, people who we fought for so let us stop with all this rhetoric already. It Never stops, Never changes, just gets worse
Obey the words of the Declaration of Independence. “when the government is no longer of, by and for the People, it is the DUTY of the PEOPLE to abolish said government”
I have said this before and i’ll say it again. The Veterans Administration, on it’s entirety, must be shut down. The day it is shut down, at one second past midnight, it will reopen under another agency name and identifier, making null and void of any union or insider “back scratching”. The new version of the “old” and “criminally” deviant Veterans Affairs will supercede AND AND ALL matters of litigation, contracts and most importantly, denials of ANY AND ALL benefits to be reevaluated under newer guidelines not associated with quotas, calculations, etc… Any and all bonuses and pay increases and retirements to VA employees from top to bottom be readjudicated on an individual basis.
It is now time to tighten the noose around the necks of VA leadership and down through the ranks. All who had even the slightest of effort in a veteran’s affairs, to be punished and adjudicated.
This is the only way.
Just like the Biden family treasonous, sadistic, and criminally deviant roll of the dice, knowing that what they were doing was and is anti-American.
Ukraine’s Santa Clause is the Biden family. Stop funding Ukraine and once the money flow stops, Biden will be convicted and arrested in the Oval Office. Same goes for Bradsher, once inside leaks become a waterfall, Bradsher is done.
Oh, and while on the subject of milotary and veterans, it is my honest and careful and thought, that the Chairmen of the Joint Chiefs be made up of the military’s four most senior enlisted…
Ben
This technology is something else. What I mean is it just invites more corruption. For example
In the CLUE Database, the information being entered is incorrect about people. And what the companies out here are viewing is not what has been inputted into this database. The companies entering information or some designated from the companies are entering fraudulent information and other people in those companies are disingenuous to the consumers when they contact the companies.
Different information in all three databases to sabotage the people. Banks are doing it too. Purposely have been entering incorrect information to increase negative risks. Exactly why some insurance companies have gone bankrupt and people losing their homes and being stuck with high costs. LexisNexis…
I included this because the IT issues are through the roof. This is how they are destroying from within. This information is relevant to what is happening in the VA.
Dirty, dirty, dirty!
Many in upper level management are tone deaf and yes we all agree that Ms Tanya is NOT the proper person for the job!
Think open mindedly about this because I know it’s commonplace and something most of you will never break. Heck, VA even sent out a memo stating that Veterans Affairs shall no longer be deemed as “The VA” any longer since “The Veterans Affairs” is not correct English. If it was “The Department of VA” that’s a different story but the infamous “The VA” is both not grammatically correct nor right on any level. Get passed it guys!
Tanya still reeks of DIRTY!
Carry on!
Agree
Ben your website deleted my response. Why? I agree!
and I am Hiring my own fraud examiner. I am tired of it.
Ben your a muckraker who has no
answers. Good on you Benny !
This is why we need more people to stand up for common sense people